VMware Cloud services supports the roles and groups authorization paradigm for managing global permissions in VMware Aria Operations for Applications. For example, a user with the Dashboards service role can manage all dashboards in Operations for Applications. This paradigm is sufficient for many of our customers.
Users with the Admin and Super Admin service roles who need finer-grained control can manage access on a per-object basis. We currently support access control for dashboards and alerts.
How Access Control Works
Operations for Applications supports granting and revoking access to dashboards and alerts.
- By default, all users can view all dashboards and alerts.
- Users with the Dashboards permission can:
- Restrict or grant access to individual dashboards from the Dashboard browser.
- Click the Share icon on individual dashboards to change who has access.
- Users with the Alerts permission can:
- Restrict or grant access for individual alerts from the Alerts browser.
- Click the Share icon on individual alerts to change who has access.
In high-security environments, users with the Admin and Super Admin service roles can change the security setting to Object Creator. After that change:
- Each new object (dashboard or alert) is visible only to the creator of the object and to the users with the Admin service role.
- The object creator and the users with the Super Admin service role can then share new dashboards with groups or users.
- If a user with the Admin or Super Admin service role changes the security setting back to allow Everyone access, then the objects that were created while the strict security setting was set, continue to be governed by access control.
Change Access for One or More Dashboards or Alerts
Privileged users can change the access setting for one or more dashboards or alerts from the Dashboards browser or the Alerts browser. The process is the same for both objects. The following steps show how to do it for dashboards.
- From the top menu bar, select Dashboards > All Dashboards.
- Select the check boxes for the dashboards you want to change. You can see the current Access settings in the Access column.
- Click +Access to add groups or users and -Access to remove groups or users.
- Enter the groups or users and click Update.
Changing Access for Individual Dashboards or Alerts
You can change access for an individual dashboard or alert from the Edit page of the object. For example, you can add access for the Finance group and revoke access for the Everyone group for a dashboard:
|
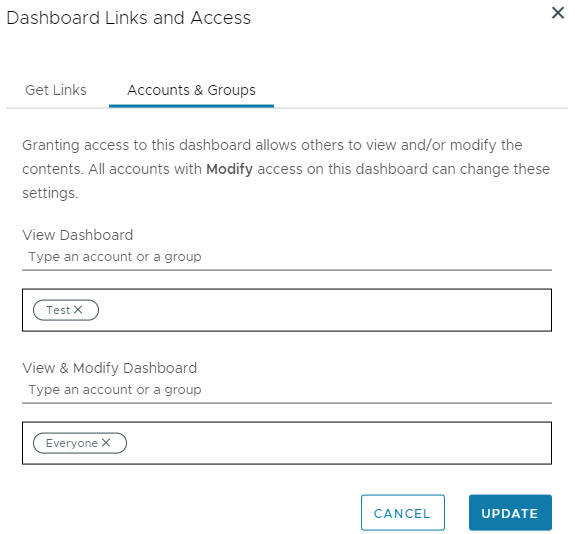 |
Change the Access Control Security Setting
Initially, all users can view all dashboards and alerts. In addition, global permissions apply:
- Users with Dashboards permission can modify all dashboards.
- Users with Alerts permission can modify all alerts.
As a user with the Admin or Super Admin service role, you can restrict access to new dashboards and alerts:
- Log in to your service instance.
- If you are a Super Admin user, enable Super Admin mode.
- From the gear icon on the toolbar, select Organization Settings.
- Click the Security tab and select Object Creator.
After the change, access to new dashboards and new alerts is initially limited to the dashboard creator and the users with the Admin or Super Admin service roles. Those users can share the objects with groups or individual users by giving View access or View & Modify access.
By default, service accounts (which includes the server to server apps in VMware Cloud services as well as the service accounts in Operations for Applications) don’t have browse permissions. However, you can also grant access for new dashboards and alerts to service accounts:
- From the gear icon on the toolbar, select Organization Settings.
- Click the Security tab, select Grant Modify Access To: Everyone and Service Accounts.
Recovering an Inaccessible Dashboard or Alert
If you can no longer access a dashboard or alert, it was either deleted (moved to trash), it was permanently deleted, or the access settings for you or a group you belong to were changed.
- If a dashboard was deleted and moved to trash less than 30 days ago, a user with the Dashboards permission can restore the deleted dashboard.
- If an alert was deleted and moved to trash less than 30 days ago, a user with the Alerts permission can restore the deleted alert.
- If a dashboard was deleted and moved to trash more than 30 days ago, or was permanently deleted, and no one, including users with the Super Admin service role, can find the dashboard. A user with the Super Admin can attempt to restore the dashboard by using the API.
- If the access settings to a dashboard or alert have changed, you can ask a user with the Admin or Super Admin service role to restore the access for you.
- If all users and groups can no longer access a specific dashboard or alert, a user with the Super Admin service role may need to check if it is in an orphaned state. A user with the Super Admin service role can make orphan dashboards and alerts visible.
Only a user with the Super Admin service role can restore dashboard permissions and attempt to restore a permanently deleted dashboard.
Make Orphan Dashboards or Alerts Visible
A dashboard or alert becomes orphaned if:
- All users and groups no longer have access to it.
- Only one user had access to it, and that user was removed.
To restore an orphan dashboard or alert:
- Log in to your service instance as a user with the Super Admin service role and enable Super Admin mode.
- From the gear icon on the toolbar, select Orphaned Objects.
- Select the orphaned dashboard or alert and share it with other users or groups.
Recover a Permanently Deleted Dashboard
A permanently deleted dashboard does not show in the trash and becomes inaccessible to all users, including the users with the Super Admin service role. As a user with the Super Admin service role, you can try to restore the dashboard by using the REST API.
- Log in to your service instance as a user with the Super Admin service role and enable Super Admin mode.
- From the gear icon on the toolbar, select API Documentation.
- Expand the Dashboard category and click the
GET api/v2/dashboard/{id}/history/{version}request. - Enter the dashboard name as the
"id"parameter. For example, if the dashboard URL ishttps://<your_instance>.wavefront.com/dashboards/MY-DASHBOARD, then the"id"that you should enter isMY-DASHBOARD. -
Enter the last known version of the dashboard as an integer.
If you don’t know the version, you can enter
1. This way, you also determine whether the dashboard"id"input has ever existed. -
Click Execute.
If the dashboard
"id"and the dashboard version don’t exist, the API call returns an error like:{ "status": { "result":"ERROR", "message":"dashboard does not exist", "code":404 } } -
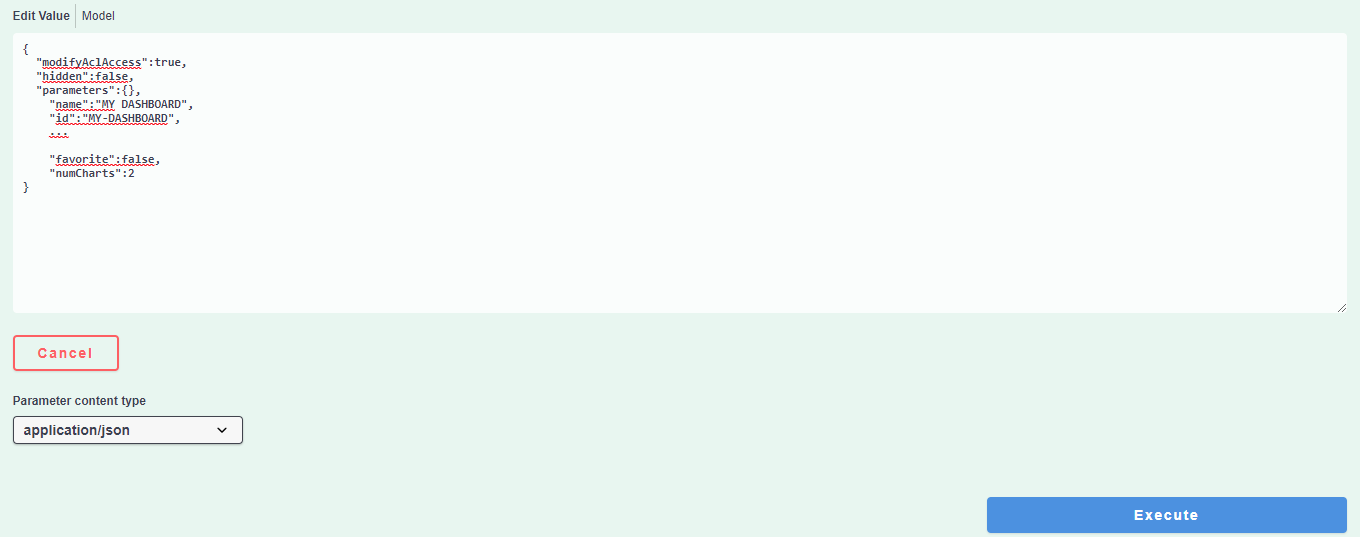
Copy the Response body of the request, that starts after
"response":up to and including the last but one closing curly bracket (}).{ "modifyAclAccess":true, "hidden":false, "parameters":{}, "name":"MY DASHBOARD", "id":"MY-DASHBOARD", ... "favorite":false, "numCharts":2 } - Click the
POST api/v2/dashboard/request. -
Paste the copied response data into the Edit Value text box and click Execute to perform the POST API call.
This will restore the dashboard.
-
Validate that the dashboard is now live again.
For example, navigate to
https://<your_instance>.wavefront.com/dashboards/MY-DASHBOARD/historyand you should now be able to review the dashboard history by using the Operations for Applications UI.